Over the past few years, there has been increasing use of large scale-botnets that have not been witnessed in the past. These botnets often have advanced features that enhance their capabilities and this makes them difficult to detect. A major DNS technique that has been used by botnets in hiding their malicious activities such as malware delivery, web proxying, malware communication, and phishing is the fast-flux.
What is fast-flux
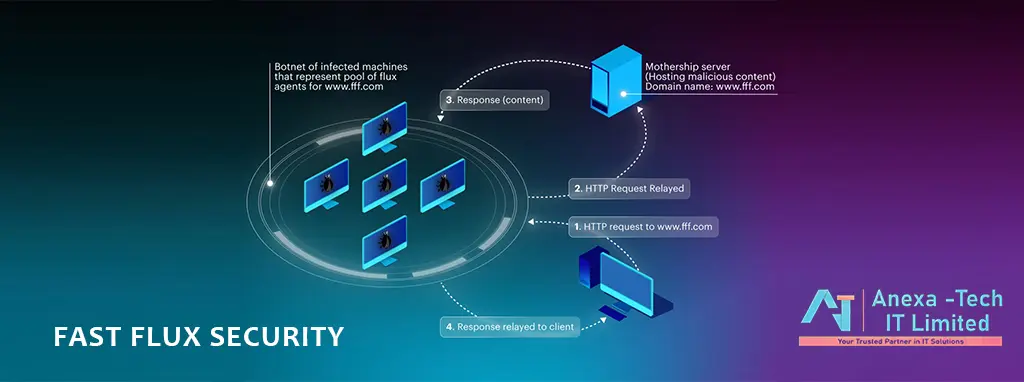
Flux security mechanism enables botnets to conceal behind compromised hosts that act as proxies and that are shifting rapidly by use of various IP addresses that are linked to acceptable domain names. By using fast-flux, botnets are able to shift quickly among the various IP addresses and this allows cybercriminals to evade detection. The fast-flux approach is primarily used to establish the connection between malware, its control server, and commands more resistant to detection by swapping IP addresses at high frequency via the change of DNS records.
There are two types of fast-flux, the single flux, and the double flux. The single flux security approach constitutes of several individual nodes with the capabilities of either deregistering or registering their addresses as part of addresses in the DNS. On the other hand, a double flux also constitutes several individual nodes that deregister or register their addresses as part of the name server DNS record list within a particular DNS zone.
Although DNS is a crucial tool that enables communication through several servers across the world to correspond IP addresses with their domains, the rapid advancement of the internet has increased its vulnerabilities to attacks. Being a fundamental tool for web functioning that allows users to get to the proper servers, applications, and sites, given its potential for abusive, the DNS traffic ought to be analyzed and monitored to keep the users safe.
The solution to DNS security
The best way to solve DNS based attacks such as fast-flux is through threat intelligence. Threat intelligence involves compiled data that is used in the identification of cyber threats. The compiled data contains information on various potential threats that organizations may face such as methods of attacks that may dismantle network infrastructure or ransomware that can be used in extorting money.
Threat intelligence can be created from both internal and external sources. External threat intelligence covers all the attacks that the internet community at large rather than targeting a particular organization. Internal threat intelligence involves the attacks that are specifically targeted at your organization and this is through the information obtained from network activities and behavior of your users. With a trustworthy service provider like Vijilan support, you can get all the information to help you solve flux security threats
Threat intelligence is a set of signs that can be used as a reference guide in solving DNS based attacks. Some of the threat information that you can get in the Vijilan labs include:
- Blocking network traffic that seems malicious through the establishment of proper network configuration.
- Identifying suspicious patterns through the provision of early insights.
- Having a better understanding of the specific risk associated with your industry by having detailed volumetric data of various malicious domains.
With the increased dependence on public networks and the complexity of various enterprise networks, maintaining a precise image of what is happening on your network has become more difficult than ever. In addition, the advanced techniques that hackers use make it essential to have a threat intelligence service provider such as Vijilan Support to identify and respond to DNS attacks as early as possible.







Leave a Reply