Latest Articles on Technology and AI
How to Secure Your WhatsApp Account from Hackers
How to Secure Your WhatsApp in Kenya: A Step-by-Step Guide WhatsApp is the most popular messaging App and has become an integral part of our daily lives in communication. It has over 2.78 billion monthly active users across 180 countries, this has made it the most popular mobile messenger app …
HOW MSSPS ARE GOING TO DELIVER SECURITY MONITORING SERVICES IN 2020
The Future of MSSPs: Delivering Advanced Security Monitoring in a Cloud-Driven World Budget constraints and a shortage of skills have led many companies to have no other option but to adopt a hybrid approach for the management of their security. As a way of dealing with the various array of …
Threat Intelligence the Road Map to Fast Flux Security
Over the past few years, there has been increasing use of large scale-botnets that have not been witnessed in the past. These botnets often have advanced features that enhance their capabilities and this makes them difficult to detect. A major DNS technique that has been used by botnets in hiding …
WHY OUTSOURCING YOUR SECURITY OPERATIONAL CENTER MAKES SENSE?
Why outsourcing your security operational center makes sense? Security Operations Center Gone are the days when identification of simple cases on a regular base was sufficient. The impact and risks of breaching incidences have been increasing over the years. The transitioning of companies of all sizes into cloud with service …
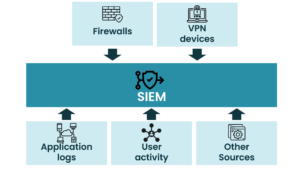
How to create SIEM using open source
How to Create SIEM Using Open Source Most of the growing organizations have adopted the use of the SIEM system given the increasing rate of cybersecurity attacks. SIEM systems have proved to be the foundation of security paradigms that help protect the IT environment from cyber threats. SIEMs are not …